The first set of questions to ask in order to assign a cyber risk profile helps to determine the important assets, including data, networks and systems, which need to be protected within the scope of the procurement. This can include assets that are controlled by a third party. You will want to understand if, and what kind of, data will be accessed or processed during the contract and the associated volume of this information. The quantity of information is an important factor as it can influence the impact if that data or information is impacted.
Data and Information
| |
Lower risk |
Moderate risk |
Higher risk |
| What kind of council's data / information assets will be accessed by third party during the contract |
Publicly available data/information |
Personally identifiable information (PII) |
PII and sensitive/financial information |
| At its greatest, what will the volume of information accessed and processed by third party under the contract be? |
Low volume |
Moderate volume |
High volume |
| Where will the data be hosted? |
Hosted on premises |
Hosted by third party in UK/friendly state |
Hosted by third party in foreign state hostile to the UK |
Networks can include both cloud and physical on-premise networks. You may need to speak with your IT team to understand the level of intended access and the existing controls in place to protect your network. If a third party has access to your network, then cyber threats could potentially exploit vulnerabilities along the supply chain and gain access to your networks through this third party.
Networks
| |
Lower risk |
Moderate risk |
Higher risk |
| What level of access / connection to the council's internal networks will be granted to third party during the contract |
No access to council's network |
Limited integration with only a specific aspect of council's network |
Fully integrated access into council's network |
Systems can include council systems, but also other third party systems, for example a housing or financial management system. Providing access to other council systems can potentially expose those systems to attack. This is an important aspect of evaluating cyber risk, because depending on the access and integration, it could bring other systems and data into the scope of the assessment. If a new product is granted full permissions on an existing service, you will need to assess that existing service to understand the aggregated cyber risk and potential impact.
Systems
| |
Lower risk |
Moderate risk |
Higher risk |
| What level of access to the council's systems will be granted to third party during the contract |
No access, or to minor systems only |
Limited access to major systems |
Full/privileged access to major/critical systems |
The length of the contract is important from a cyber security perspective as the supply chain cyber security landscape is constantly changing and evolving. A long-term term contract could have significant security vulnerabilities introduced over time, so appropriate controls would need to be put in place to mitigate against these over the full length of the contract.
The value of the contract can also be closely linked with the impact on the council and connected stakeholders in the event of a cyber incident.
It is also important to understand that the contract scale is just one of many influencing factors. The supply chain includes all acquired services and products, even if those are open source or free to use. Free digital services and products could cause a cyber incident, causing catastrophic damage to your organisation.
Contract scale
| |
Lower risk |
Moderate risk |
Higher risk |
| How long will the contract last? |
Short-term |
Mid-term |
Long-term |
| What is the value of the contract (financial/strategic) |
Low value |
Mid value |
High value |
It may be worth noting that questions are important to consider, but are mostly applicable to existing contracts, and would not necessarily apply to new procurements where the supplier is not yet known. The purpose of this section is to help evaluate the potential cyber risk and subsequently apply controls, not to exclude suppliers based on these criteria.
With that said, the length of the contract is important from a cyber security perspective, because with the supply chain cyber security landscape constantly changing, a long-term term contract could have significant security vulnerabilities introduced over time. As such, appropriate controls would need to be put in place to mitigate against this.
The value of the contract may be closely linked with the impact on the council and connected stakeholders in the event of a successful cyber incident.
Determining supplier risk
| |
Lower risk |
Moderate risk |
Higher risk |
| Where would the supplier be based during the contract and which states have they links with? |
UK |
EU or other friendly states |
Foreign state hostile to the UK |
| Are there any known breaches with the supplier? |
No |
Yes - where adequately identified, responded to and recovered from |
Yes, where not adequately addressed |
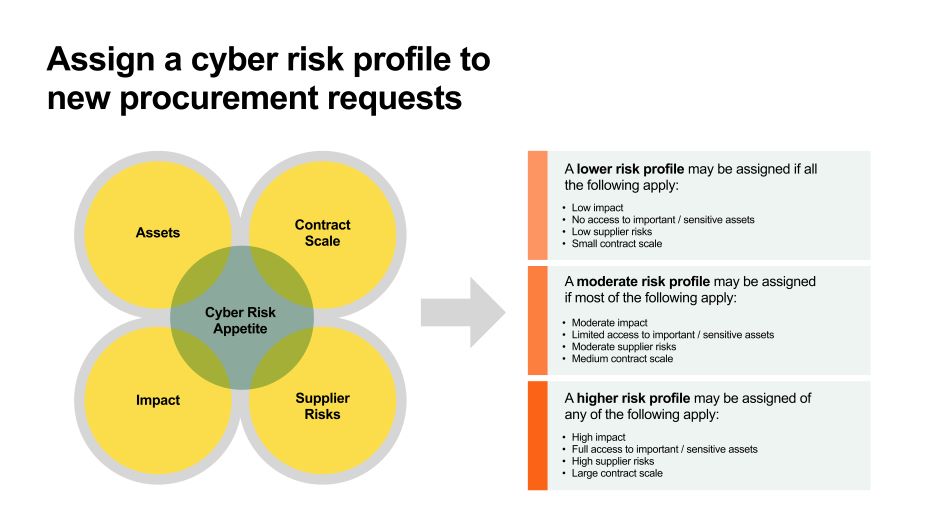
Another set of potential questions to ask in order to assign a risk profile would be questions that determine the level of impact a cyber incident could have on your local council organisation, including related stakeholders, such as council residents. Note that how you would categorise the impact in each area would be based upon your council’s cyber risk appetite.
The impact of a cyber incident is normally directly correlated with the assets that are affected by the incident. When evaluating the impact, you need to consider what would be the affected assets, and how would they be impacted? Could an incident impact the confidentiality, integrity or availability of those assets? If yes, then what would be the business impact that results from that?
Questions to consider here include:
Impact of cyber attack
| |
Lower risk |
Moderate risk |
Higher risk |
| Loss of trust / reputational damage |
None/very limited |
Some |
High |
| Disruption to business or local services |
None/very limited |
Some |
High |
| Financial impact |
None/very limited |
Some |
High |
| Legal burden |
None/very limited |
Some |
High |
Depending upon the type of service or product request, you may not have all of the information readily available to assess the full questionnaire. Additionally, the level of risk may vary based on council type, size, budget, and overall procurement strategy. You will need to work closely with the internal product, service, IT and security teams in order to fully assess the request. Consult the NCSC Principles for more guidance on risk assessments.